About The Author
Punch Through
We’re a team of engineers who obsess over making connected things actually work — reliably, securely, and without the handwaving. From BLE to backend, we build the software and systems behind connected medical devices and custom connected products that can’t afford to fail.

Explore Articles by Punch Through

How to Use LightBlue to Debug Your Firmware
When integration testing breaks down, it’s not always obvious whether the problem lives in your firmware or somewhere else. This guide shows you how to debug BLE firmware with LightBlue step by step, from advertising and connections to GATT discovery, notifications, writes, and pairing.
Read More
Is Your Connected Device Architecture Ready for Continuous Oversight?
FDA’s expanding TAP Program signals a shift toward continuous oversight for connected medical devices. That shift changes what teams need to design for: not just functionality, but architecture that can prove performance, traceability, and control across the product lifecycle.
Read More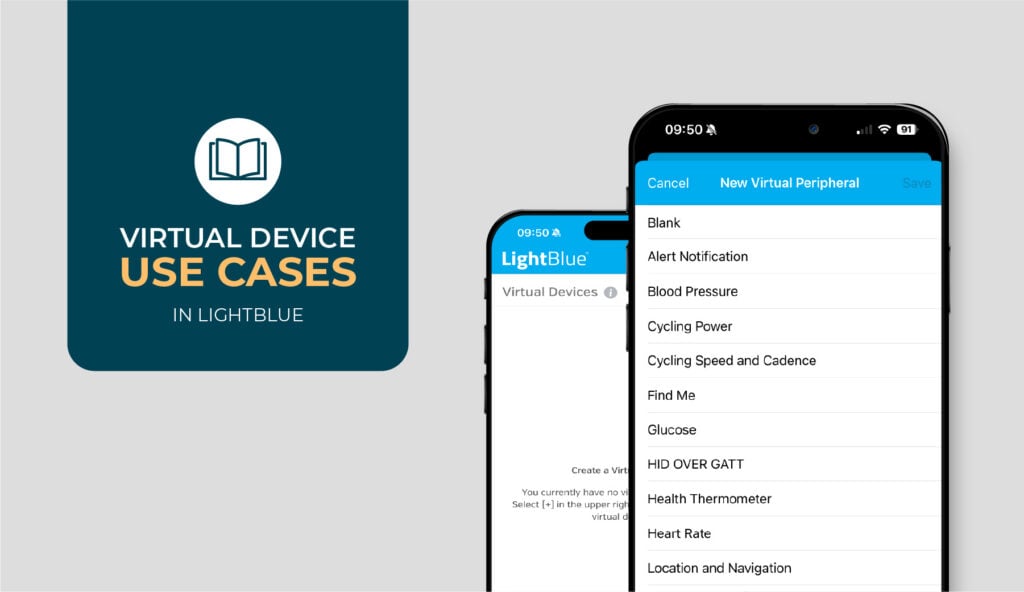
When (and When Not) to Use Virtual Devices in LightBlue
Should you test against a simulated peripheral or real hardware? This article breaks down when LightBlue Virtual Devices are useful and when relying on them can hide integration issues you need to catch.
Read More
How Much BLE Security Does Your Device Actually Need?
Not every BLE device needs maximum security. A fitness tracker, smart lock, and medical device face very different risks. This article walks through a practical framework to help you determine the right level of BLE security for your product based on regulation, data sensitivity, threat model, and user experience tradeoffs.
Read More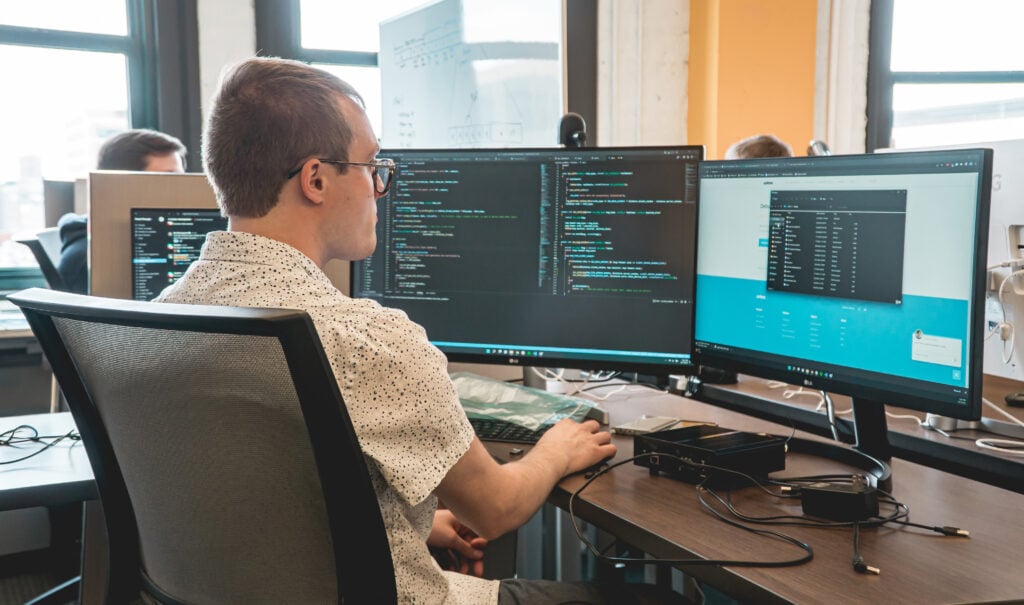
Understanding BLE Security Boundaries: What It Protects and What It Doesn’t
BLE encryption and authenticated pairing secure over-the-air communication, but they don’t protect data once it reaches your app or cloud. Learn where BLE security stops and when you need TLS, end-to-end encryption, and user authentication.
Read More
Understanding BLE Connections: How to Choose Advertising, Scanning, and Connection Parameters
Choosing the right BLE connection parameters directly impacts discovery speed, reliability, and battery life. This article explains how advertising, scanning, and connection intervals work together and how to tune them for real-world performance.
Read More
How to Use LightBlue Virtual Devices
When hardware isn’t available, Virtual Devices in LightBlue let you keep moving. Simulate BLE peripherals, test app behavior, and explore GATT designs without depending on physical devices.
Read More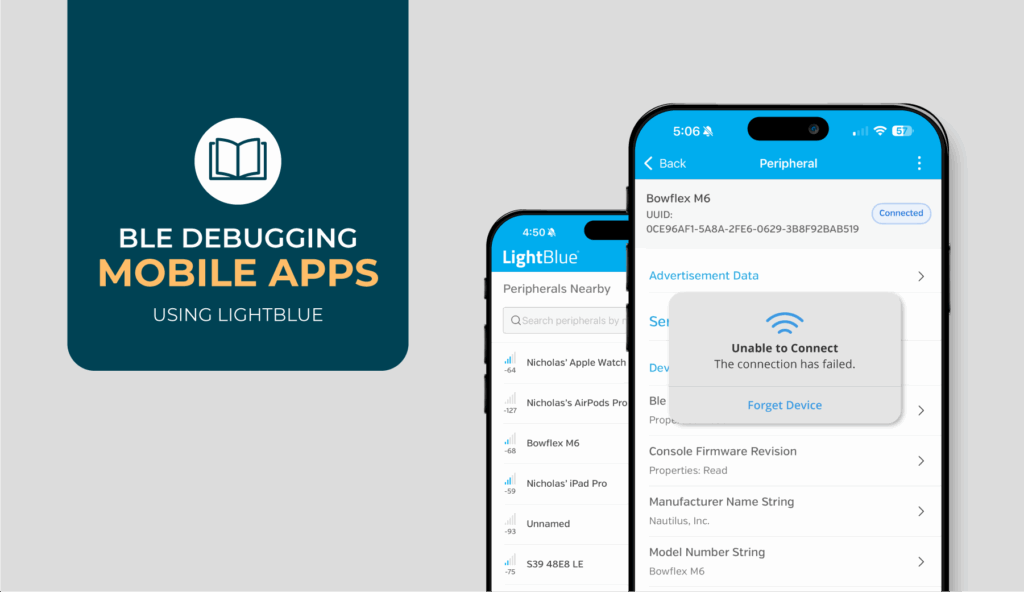
How to Use LightBlue to Debug A BLE Mobile App
When your BLE mobile app won’t connect or starts behaving unpredictably, it’s hard to know whether the bug is in your code or the device. This article shows how LightBlue helps you isolate the problem and debug it faster.
Read More
Always-Connected vs. Dynamic BLE: Which Strategy Fits Your Product?
Should your BLE device stay connected at all times or only link up when needed? We break down the pros, cons, and use cases for always-connected and dynamic BLE to help you make a confident architectural decision early in development.
Read More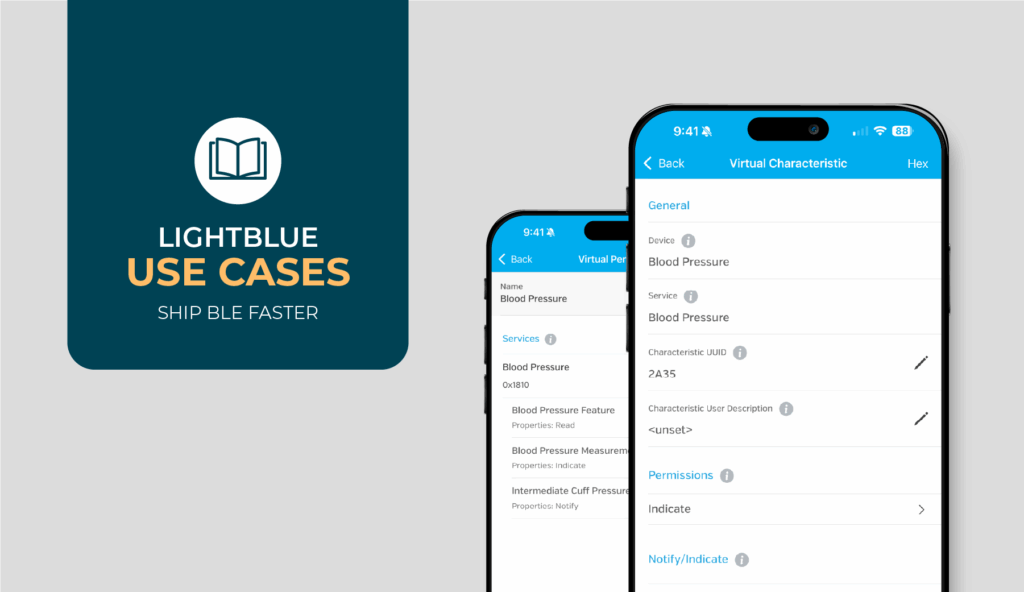
LightBlue Use Cases to Ship BLE Faster
Practical ways to simulate devices, reproduce connection issues, verify security, stress-test performance, and debug central/peripheral roles.
Read More